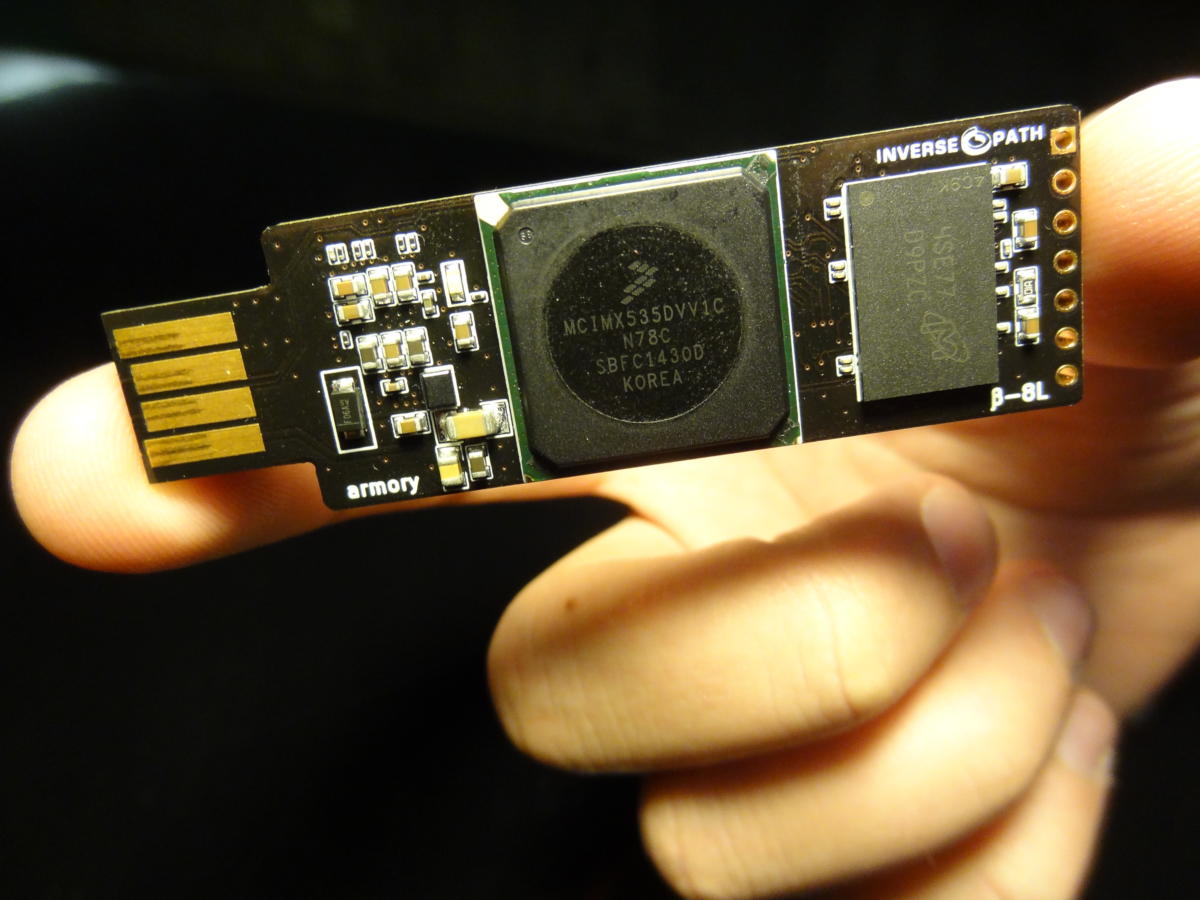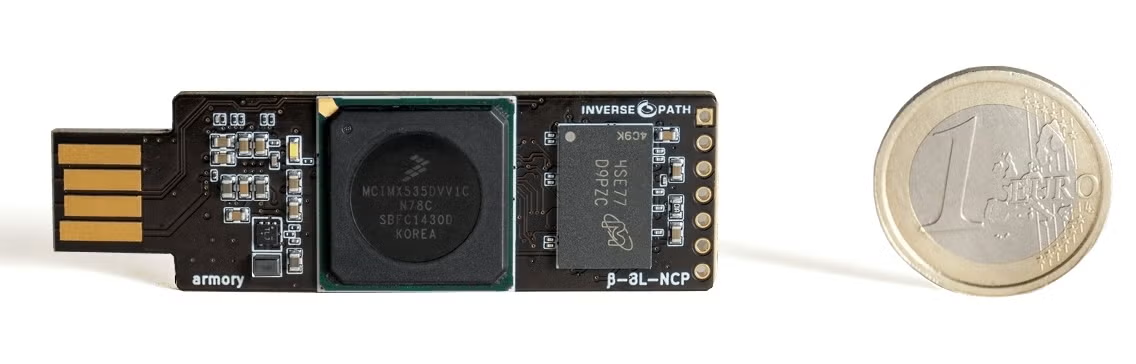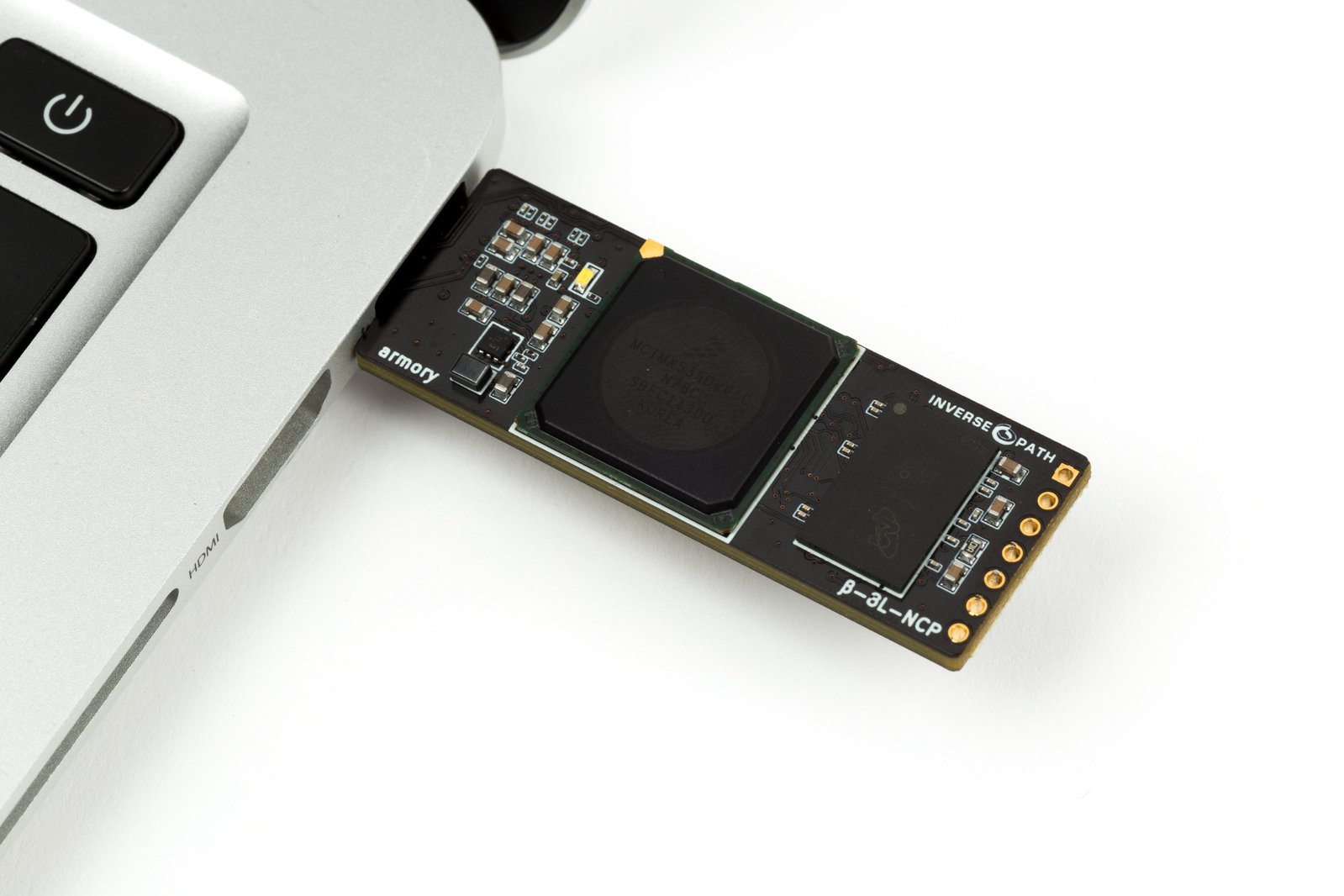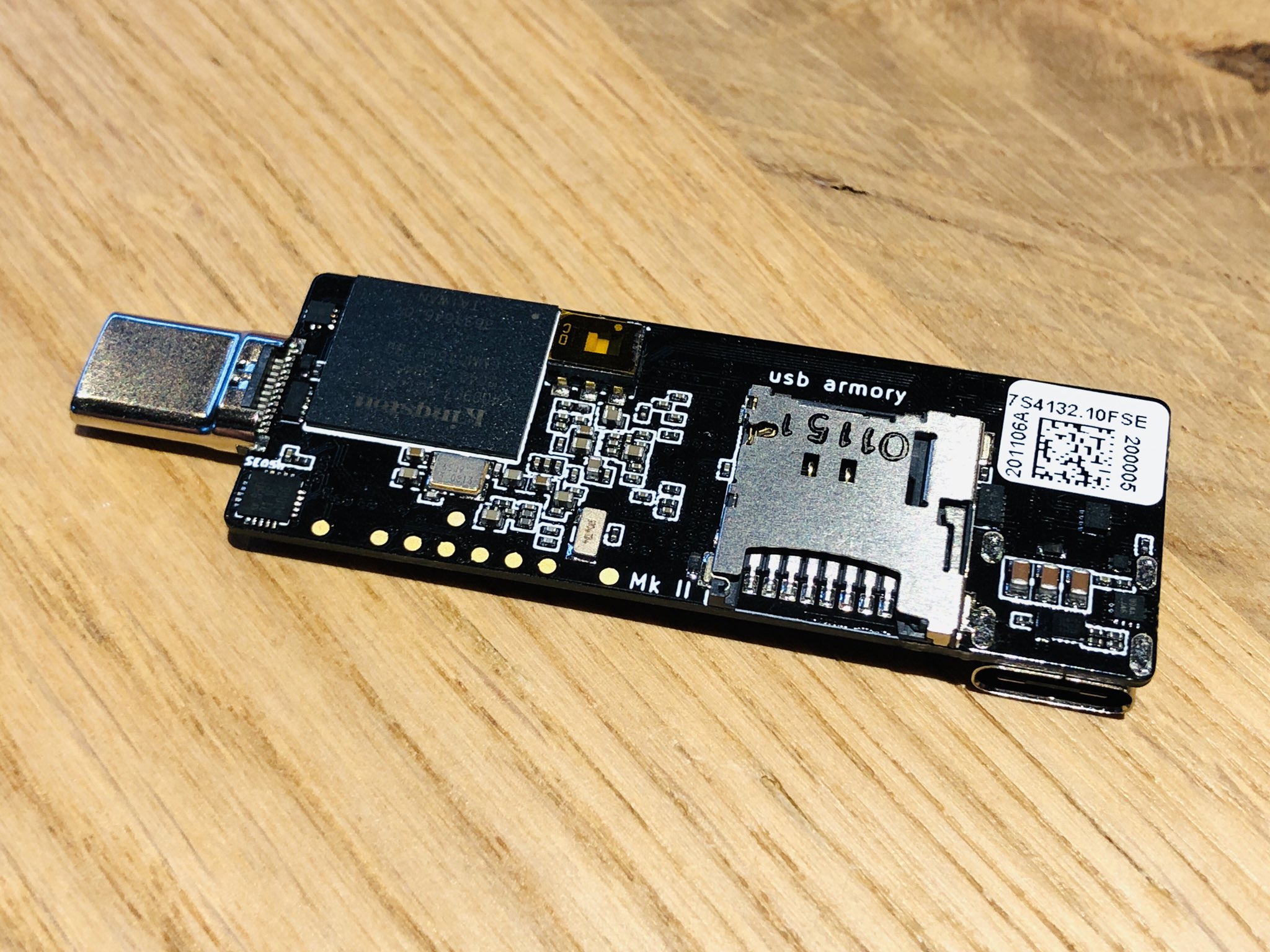
mikko on Twitter: "WithSecure's USB armory does post-quantum cryptography in space. Because in space, no one can here you do post-quantum cryptography. https://t.co/9FIVWl3n2q https://t.co/nZMqje7QGY" / Twitter

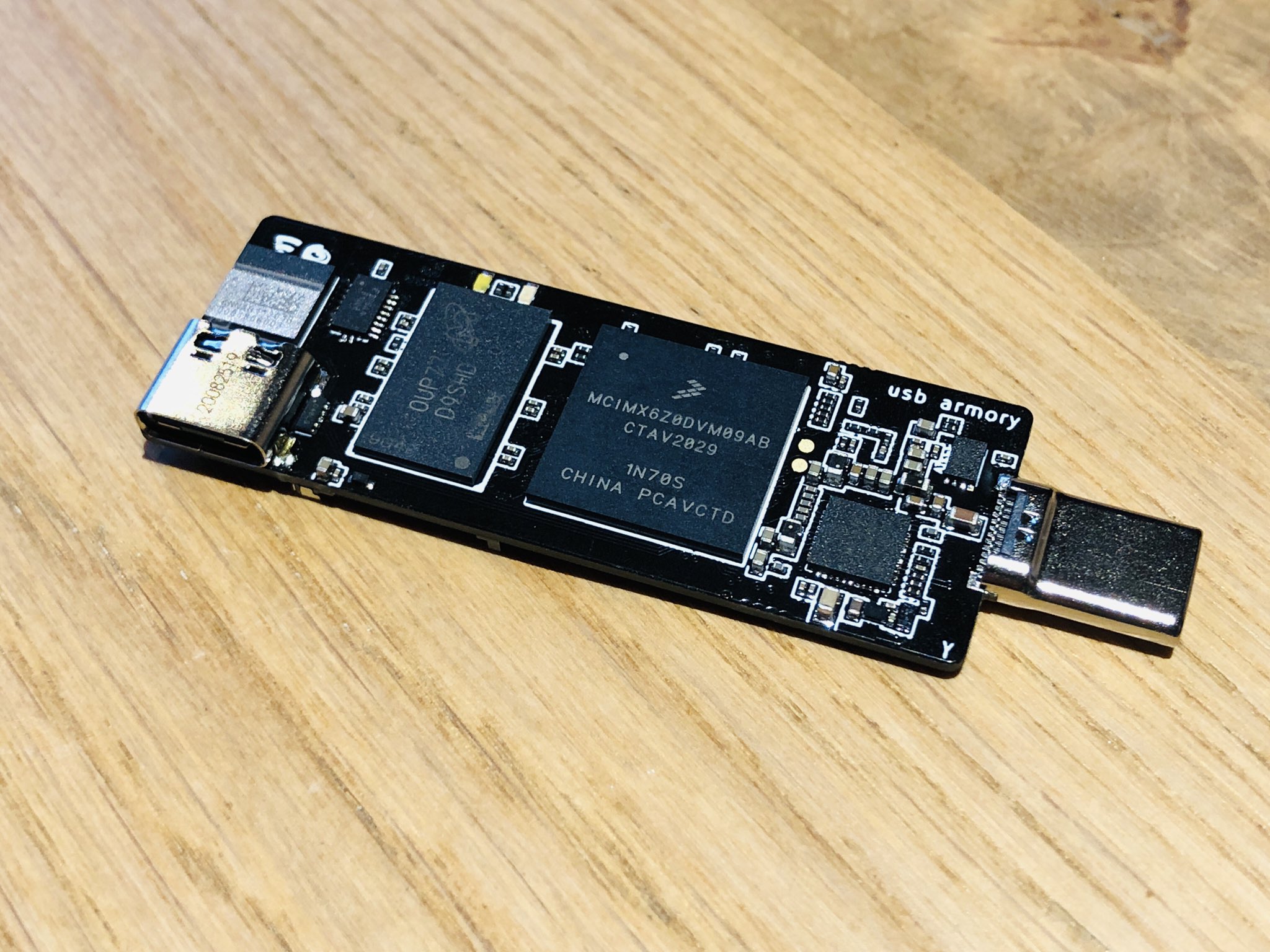
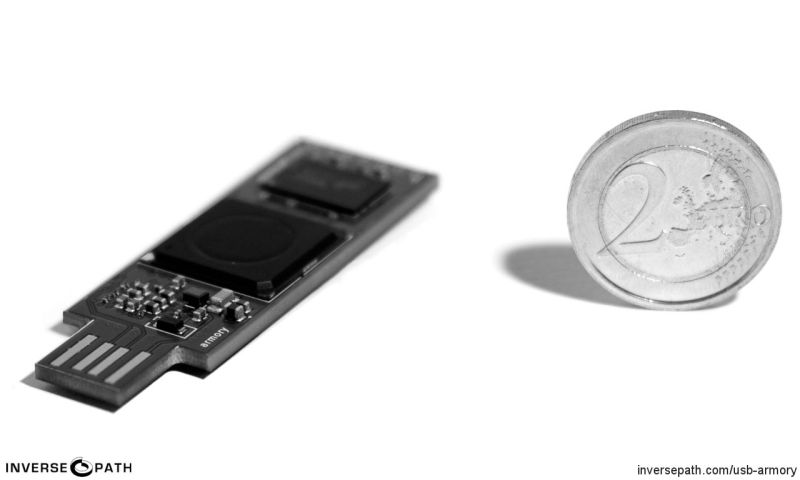
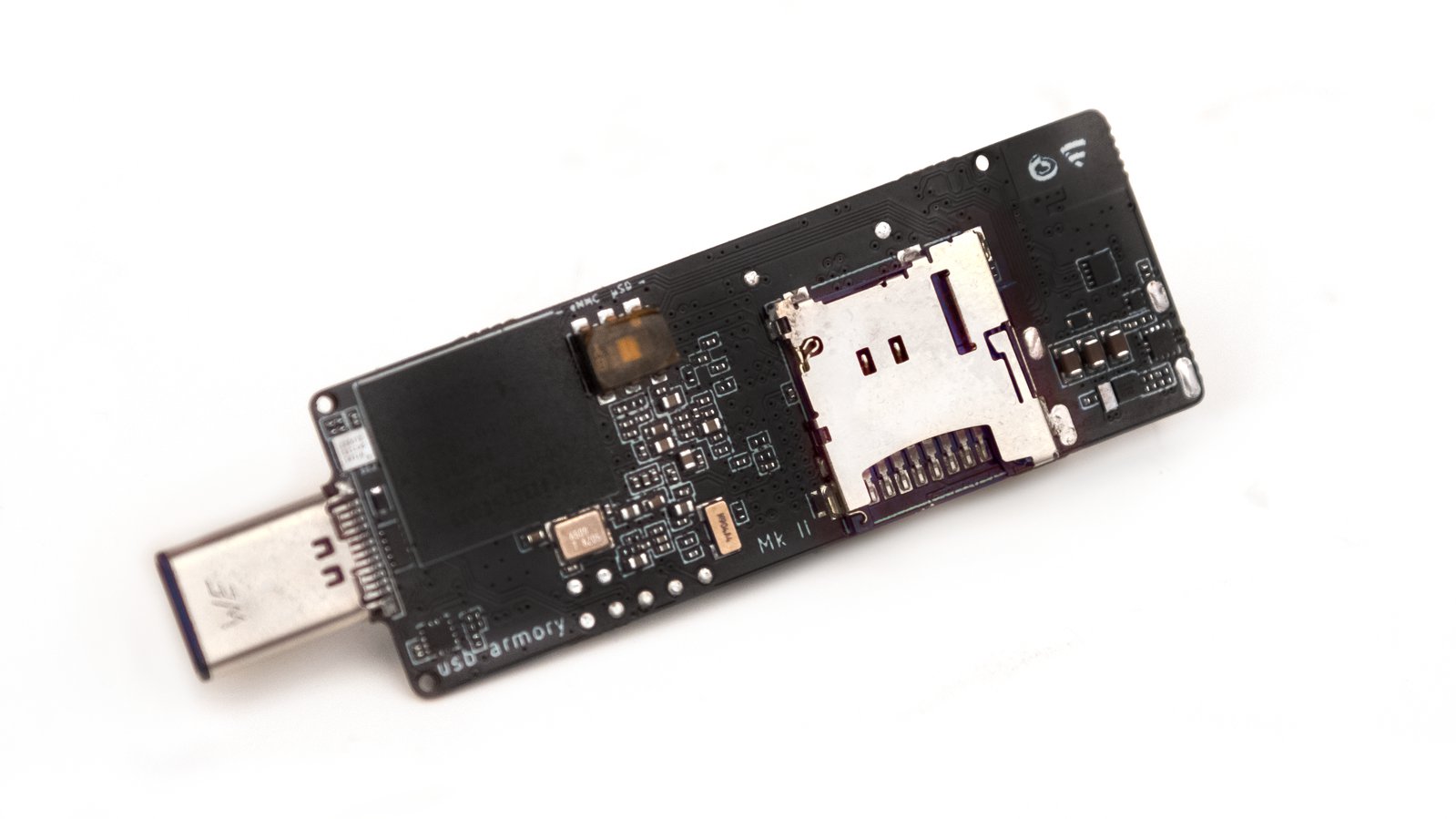
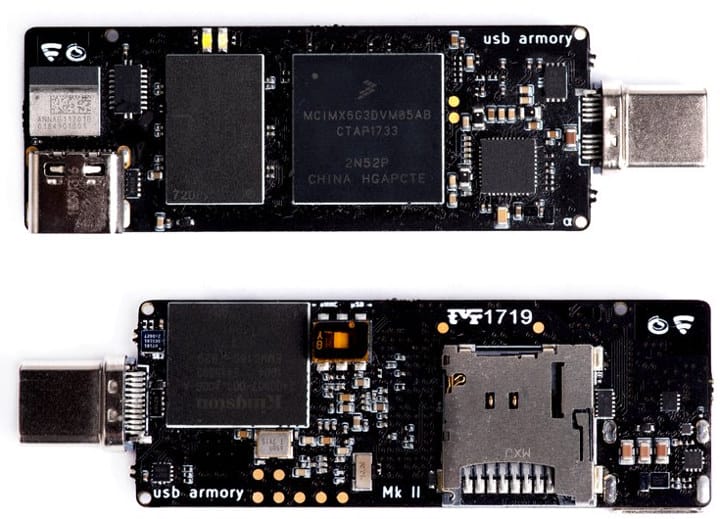
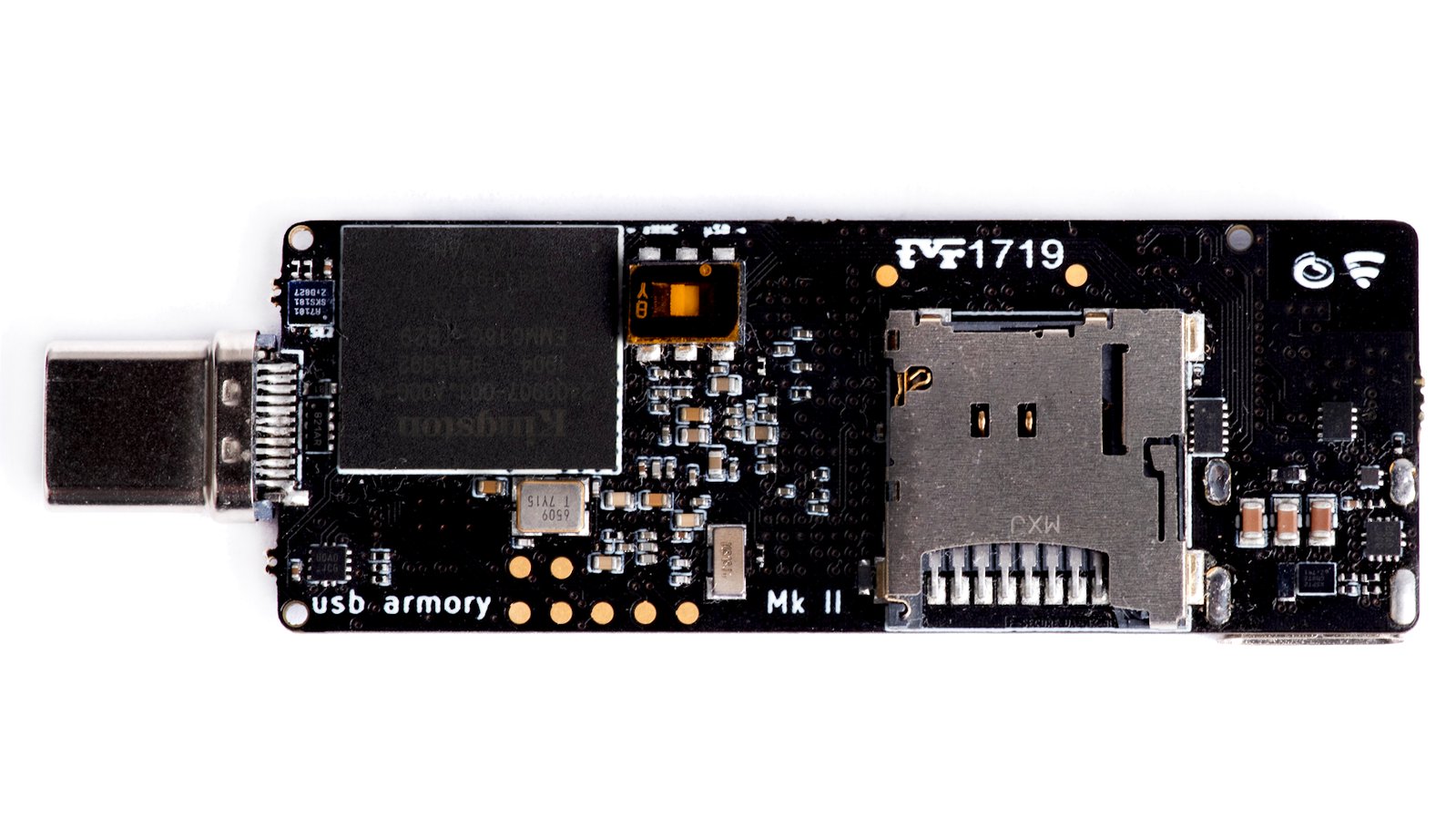
WithSecure™ on Twitter: "NEWS: F-Secure's USB armory Mk II packs industrial-grade security into a computer the size of a thumb https://t.co/97r75u7bfk" / Twitter